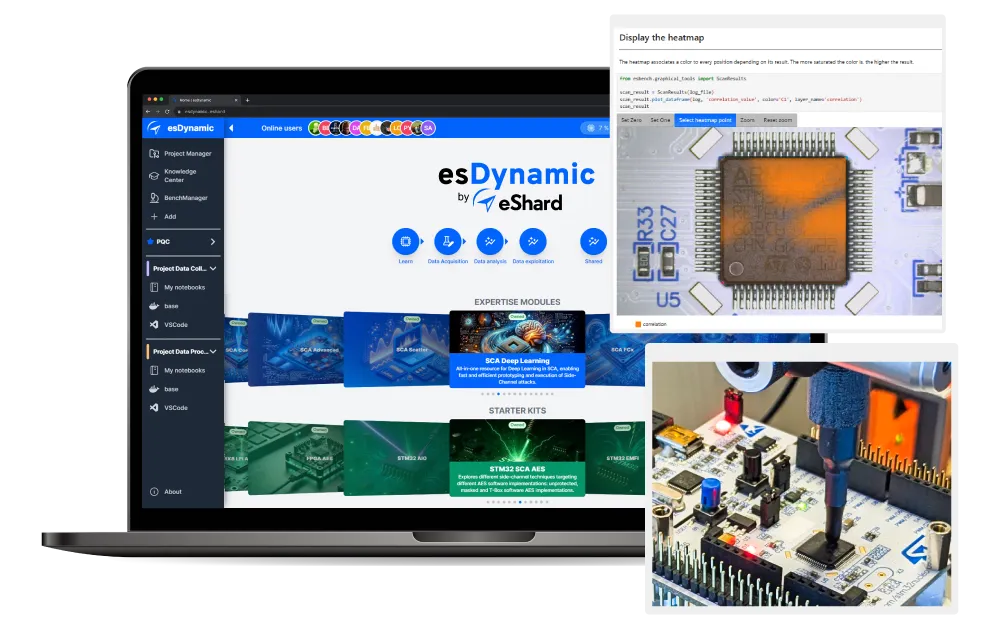
One environment for all investigations

Project-based organization
Each investigation is a project with its own datasets, tool configurations, team access, and findings. Switch between analyses without rebuilding your environment.
Open data science
environment
Leveraging JupyterLab technology, develop and bring your own scripts, your analysis is a notebook. Connect to your computing infrastructure, using server, GPUs or distributed solutions. The platform adapts to your methodology, not the other way around.
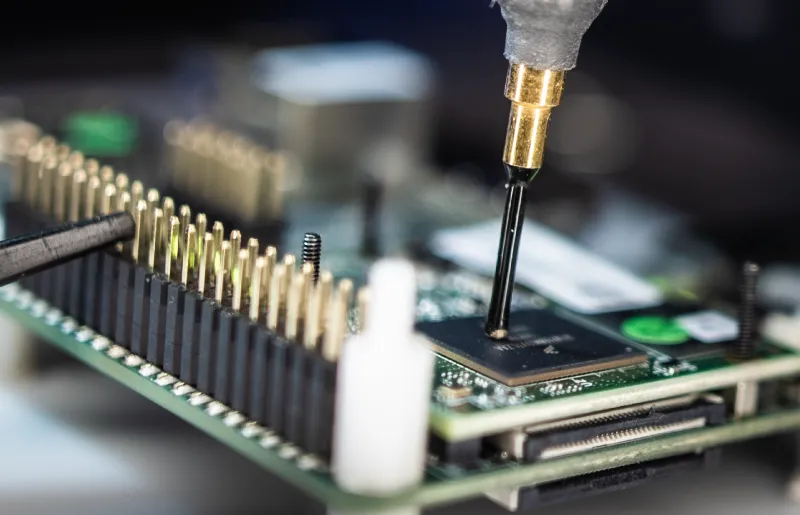
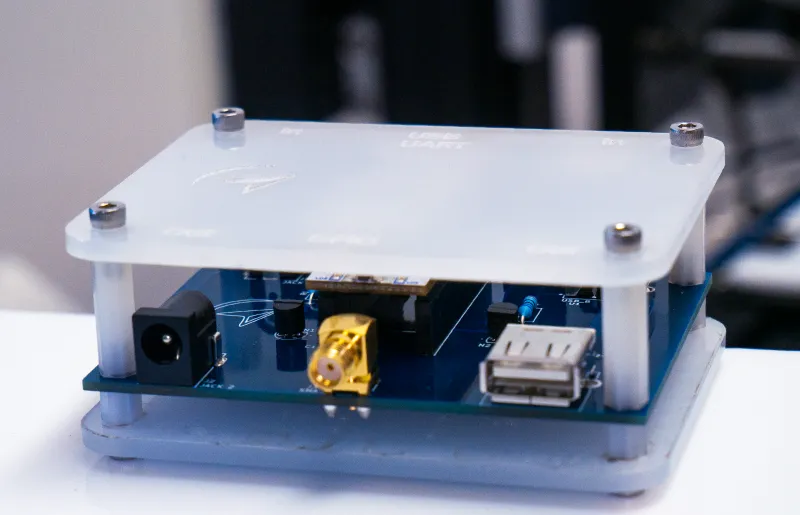
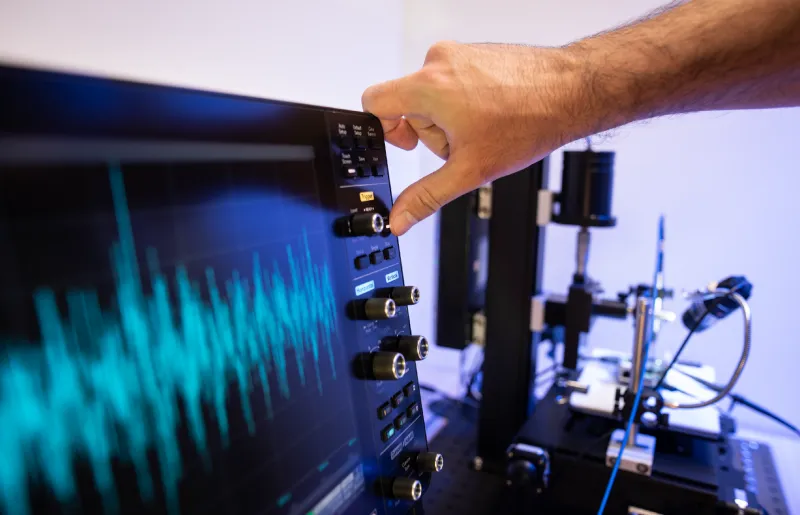
Agnostic hardware
instrumentation
Integrate and control any hardware setup. Oscilloscopes, fault injectors, probes, or custom equipment all fit into the same workflow, accessible remotely by multiple analysts.
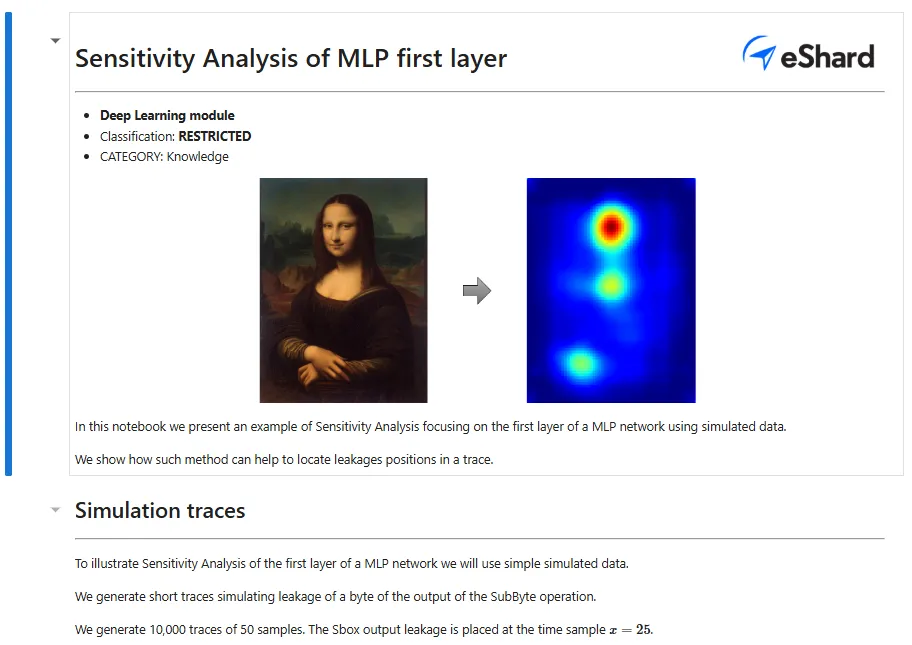
Source of incremental
knowledge
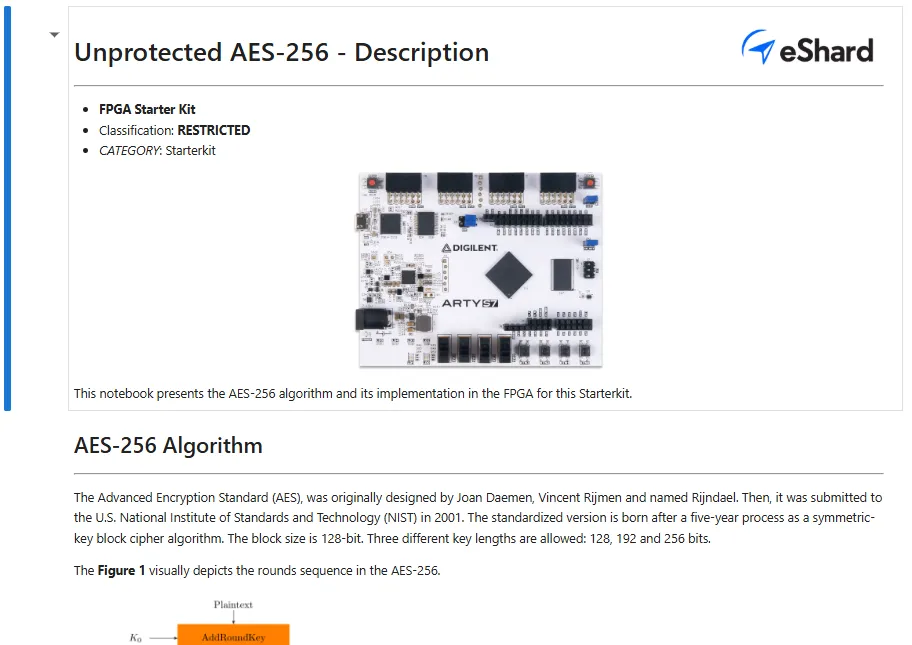
Leverage our ready-to-use knowledge notebooks built from real-world attacks. Execute automated campaigns, reuse existing workflows, and extend them with your own work.
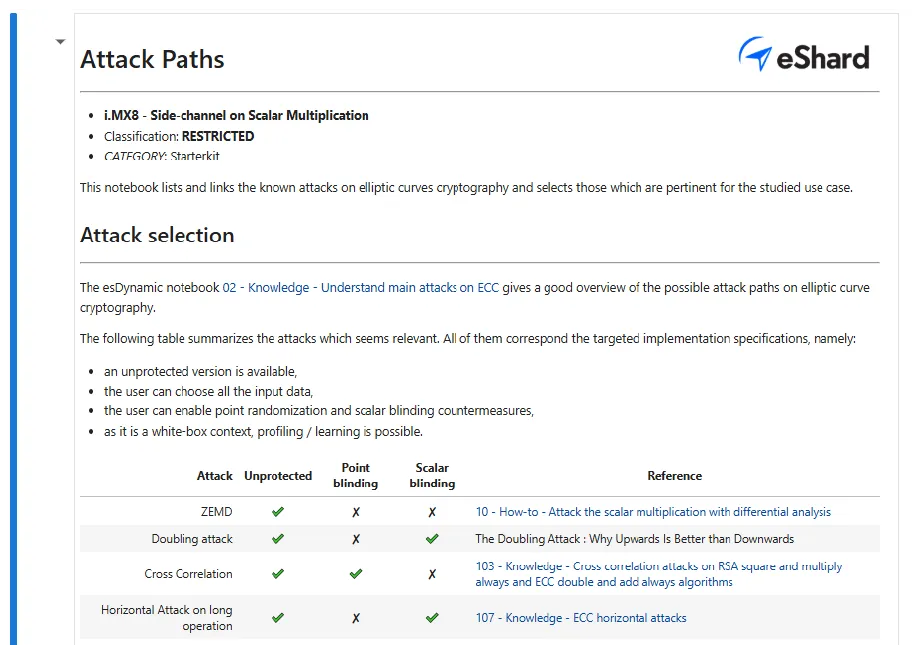
Start from proven methodologies
Access ready-to-use security methodologies, extend them with your own findings, and build reusable attack templates that empower your entire reverse engineering team.
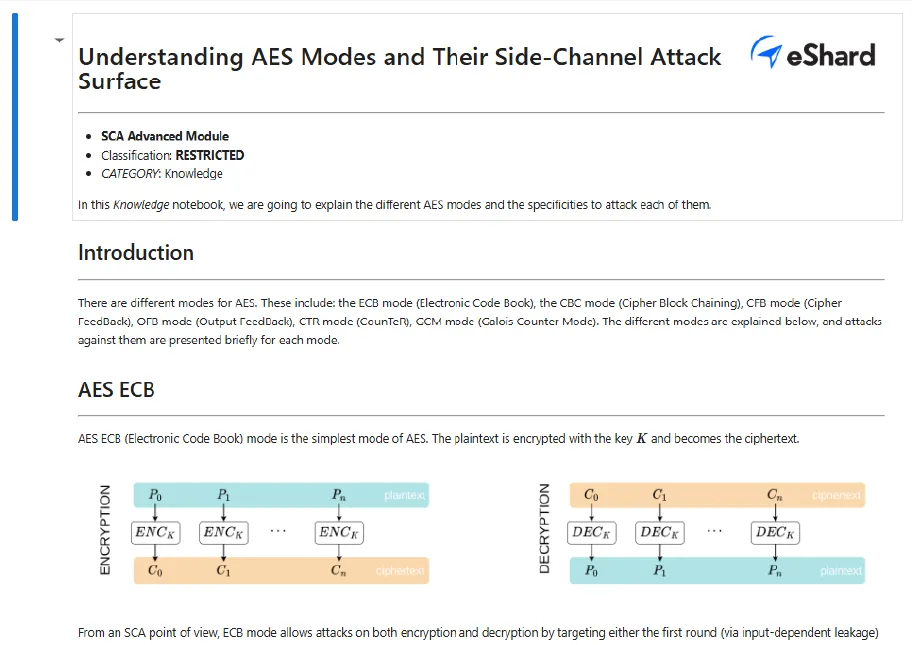
Advanced Side-Channel Analysis
High-order combinations, horizontal analyses, collision attacks, and lattice attacks targeting ECC, RSA, and hardened symmetric algorithms.
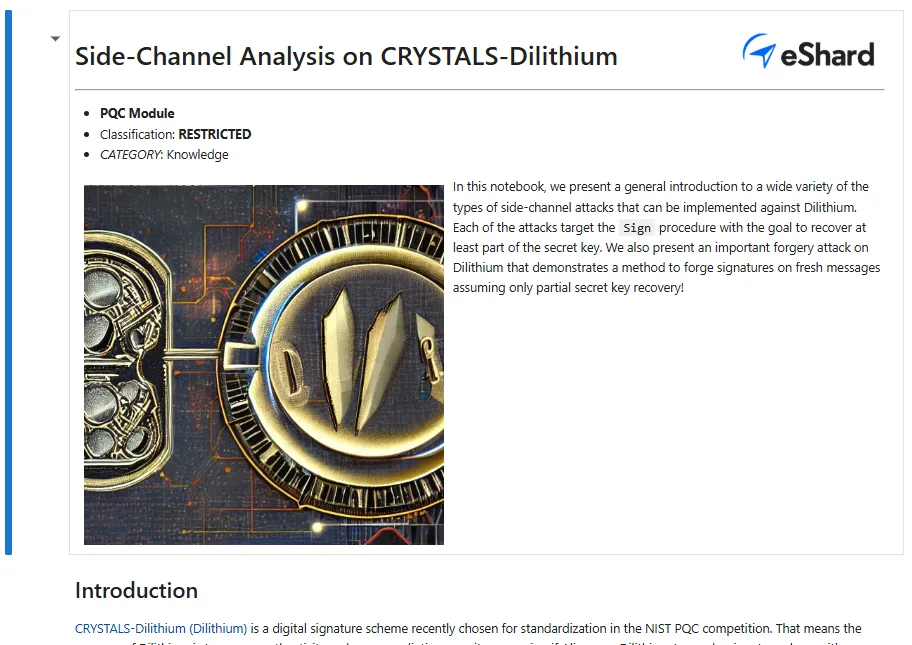
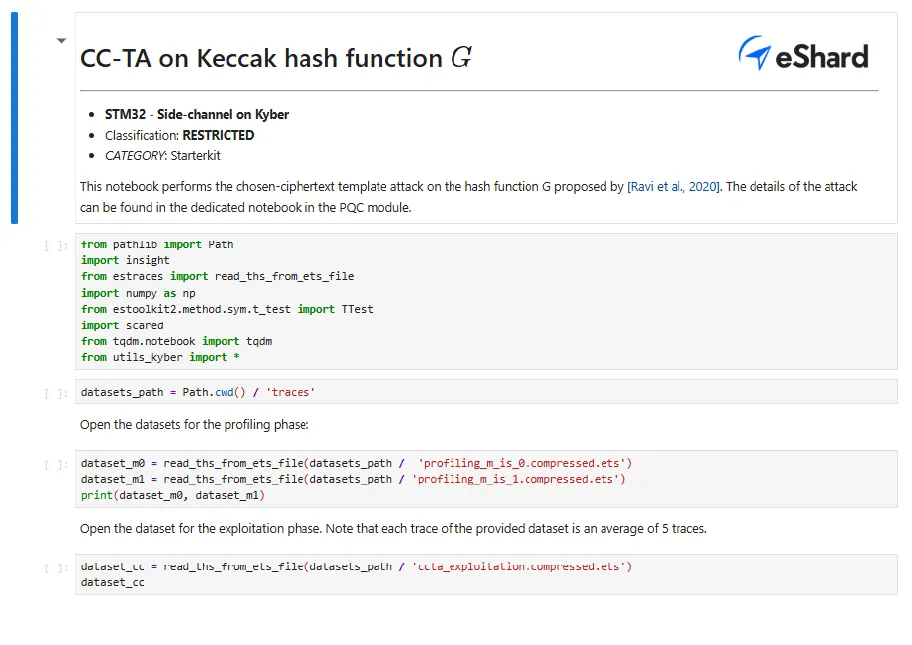
Post-Quantum Cryptography (PQC)
Toolsets to analyze side-channel leakages and execute attacks against ML-KEM (Kyber), ML-DSA (Dilithium), SLH-DSA (SPHINCS+), and Falcon.
Expertise in SCA on-demand
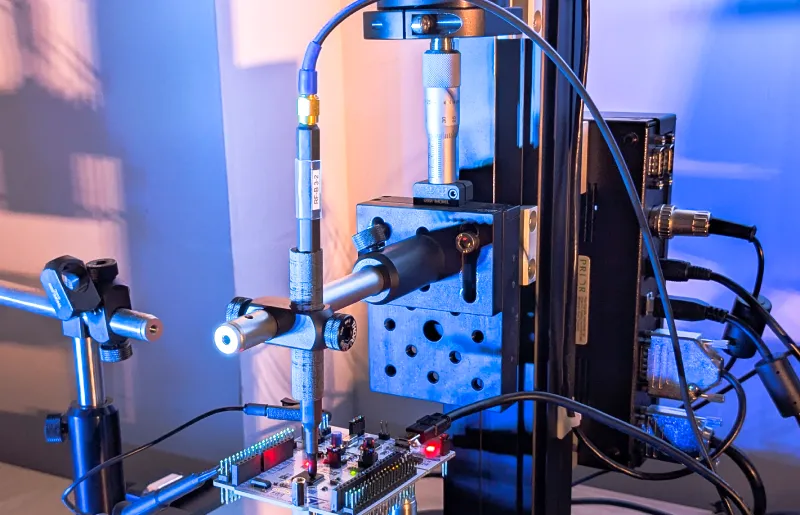
Hardware Security Assessment
We evaluate secure elements, ASICs, SoCs, and FPGAs in either white-box or black-box scenarios. Receive actionable insights and fully detailed reports enriched with replayable Jupyter notebooks.
Security Training & Coaching
Accelerate your team's proficiency with remote or onsite coaching. We guide your engineers to master advanced, high-order methodologies.
Upgrade Your SCA Hardware Security Lab
Discuss your current lab setup, specific target architectures, or upcoming hardware evaluation projects with our engineering team.
Frequently Asked Questions
esDynamic is a hardware-agnostic platform. It seamlessly integrates with your existing third-party oscilloscopes, motorized XYZ stages, and near-field EM probes, allowing you to upgrade your side-channel analysis lab without vendor lock-in.
Processing millions of traces requires high-performance computing. esDynamic leverages built-in GPU acceleration and distributed computing to efficiently align, filter, and process massive trace datasets for heavy statistical computations without performance bottlenecks.
Yes. eShard provides a dedicated Expertise Module for PQC, giving your team optimized tools, datasets, and executable attack scripts to analyze side-channel leakages on next-generation algorithms including ML-KEM (Kyber), ML-DSA (Dilithium), SLH-DSA (SPHINCS+), and Falcon.
We offer flexible pathways to bridge the knowledge gap. You can rapidly upskill your internal team using our hardware Starter Kits and expert-led esCoaching (remote or onsite). Alternatively, you can outsource complex physical evaluations directly to our state-of-the-art SCA lab.