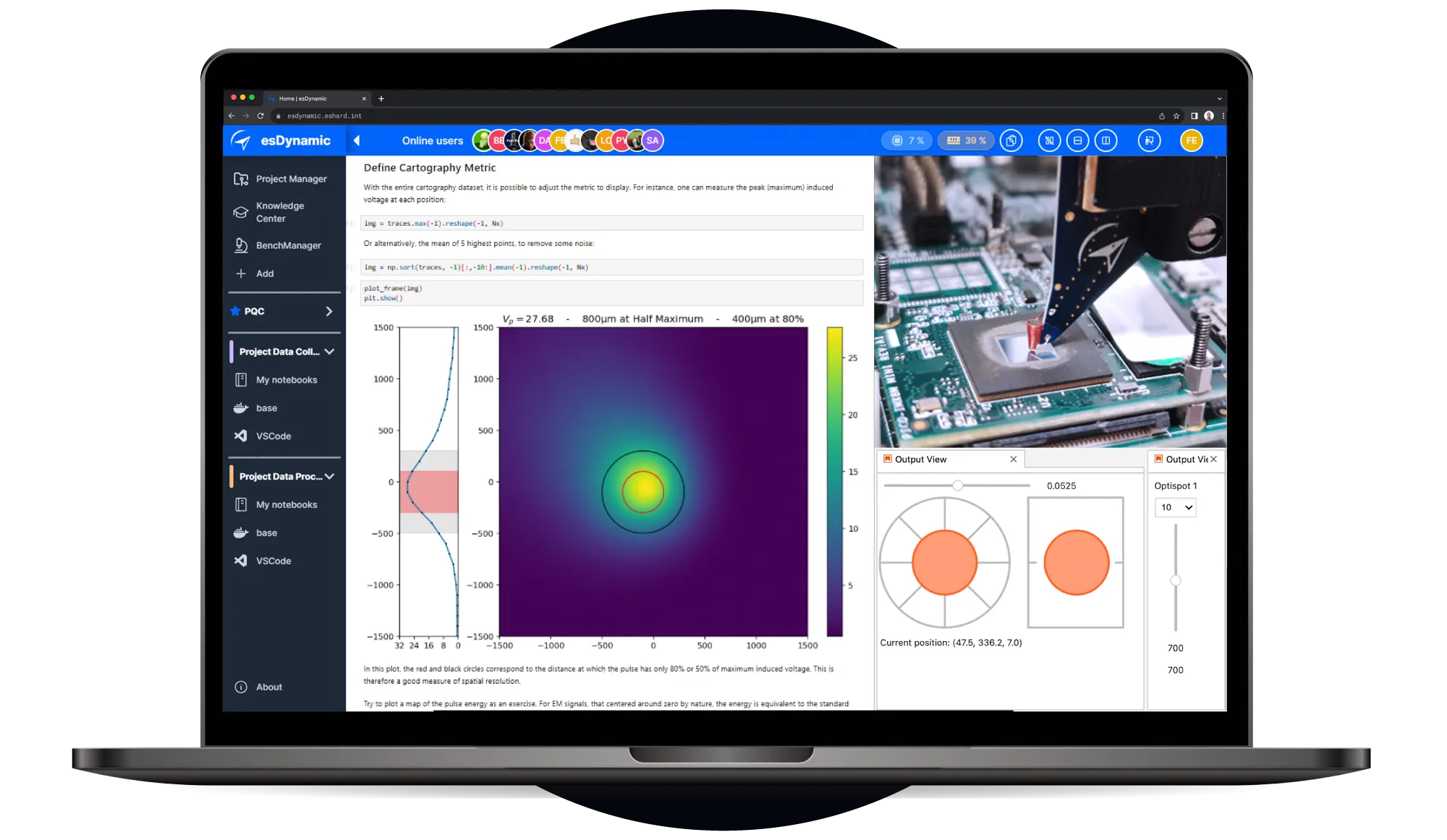
One environment for all investigations

Unified EMFI Workflow
Manage your entire process from IC characterisation to fault exploitation. Set up your bench, manage scanning against different parameters, compile logs and run the exploitation.
Open data science
environment
Your engineering team can share a central workspace to co-edit Jupyter notebooks, analyze results, and even control the hardware equipment remotely in real-time.
Agnostic hardware
instrumentation
Easily connect and control your existing oscilloscopes, pulse generators, and motorized stages from any vendor alongside eShard hardware.
Expert Knowledge
Jumpstart your campaigns with ready-to-use Jupyter notebooks, designed to guide you through spatial cartography, parameter mapping, and multi-fault injections.
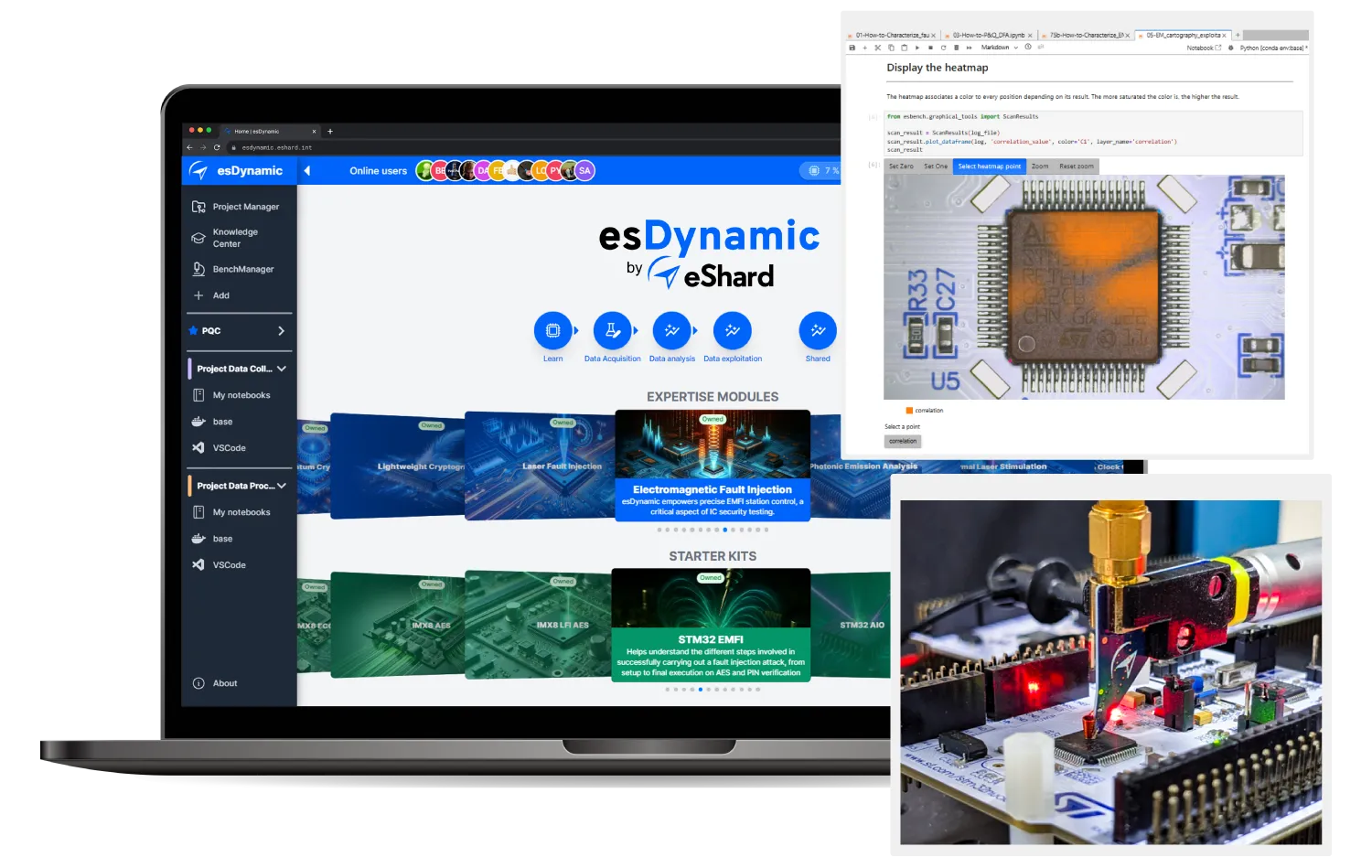
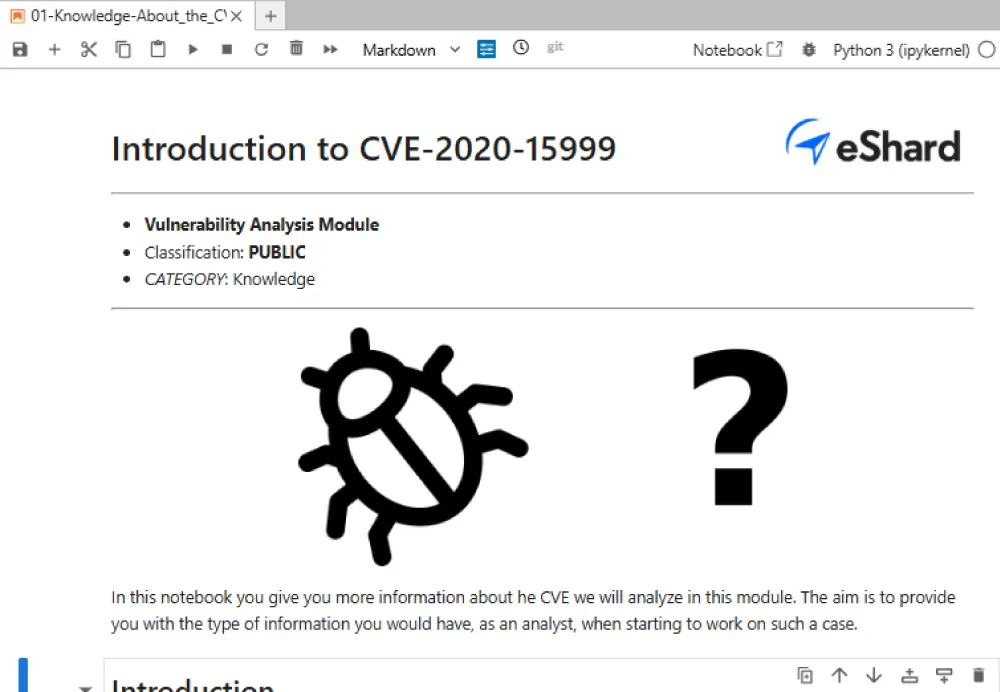
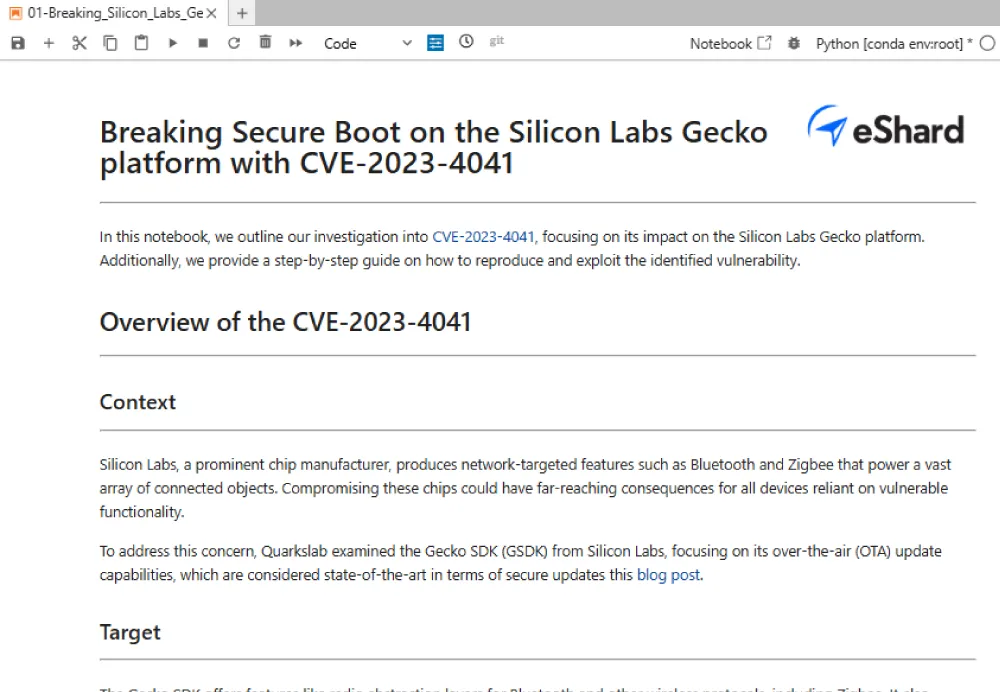
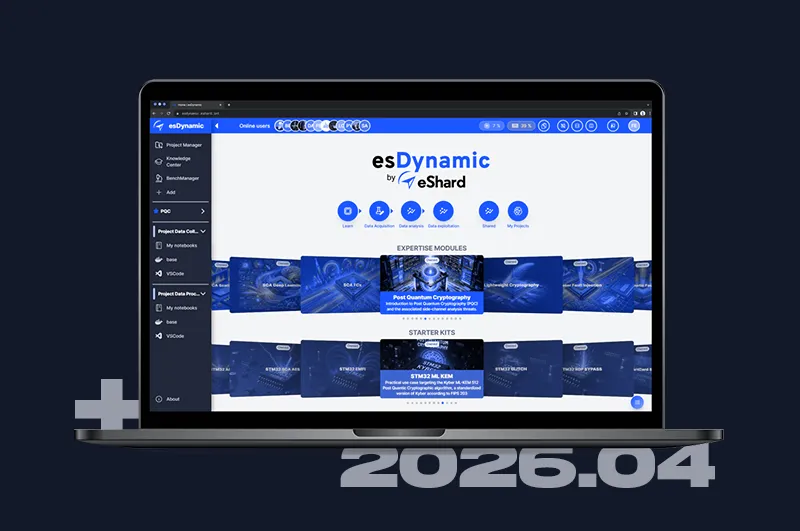
Start from proven methodologies
Leverage our team's extensive hardware analysis experience. Our Expertise Modules provide highly educative, executable Jupyter Notebooks tailored specifically for assessing modern devices.
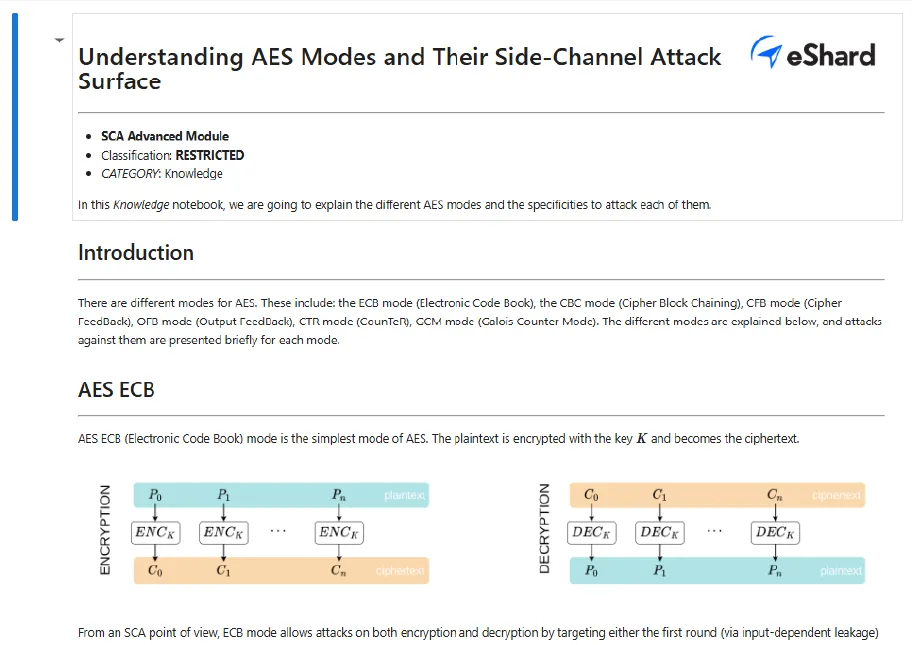
Differential Fault Analysis (DFA)
Step-by-step scripts to exploit faults, analyze physical effects, and uncover cryptographic secrets from DES, AES, and RSA algorithms.
AES key recovery — i.MX8 SoC
Fault CPU registers and ARMv8 instructions to retrieve AES keys across software, ARMv8 CE, and hardware implementations.
On-Demand EM Fault Injection Expertise
Hardware Security Assessment
We evaluate secure elements, ASICs, SoCs, and FPGAs against state-of-the-art fault injection techniques. Receive actionable insights and fully detailed reports enriched with replayable Jupyter notebooks, delivered by our seasoned analysts.
Security Training & Coaching
Accelerate your team's proficiency with remote or onsite coaching. We guide your engineers from basic glitching theory to executing fully automated, multi-fault campaigns.
Upgrade Your EMFI Hardware Security Lab
Discuss your current lab setup, specific target architectures, or upcoming hardware evaluation projects with our engineering team.
Frequently Asked Questions
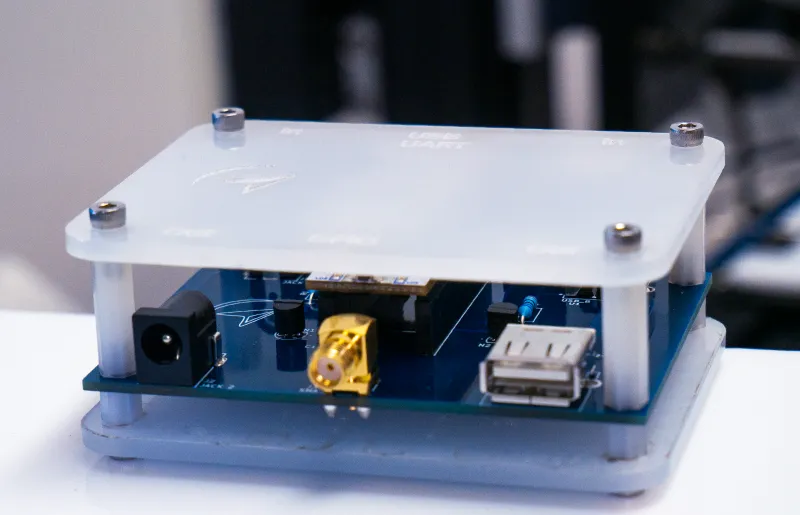
esDynamic is hardware-agnostic, allowing you to pilot third-party oscilloscopes, pulse generators, and XYZ stages from any vendor alongside eShard hardware through a unified Python API or dashboard.
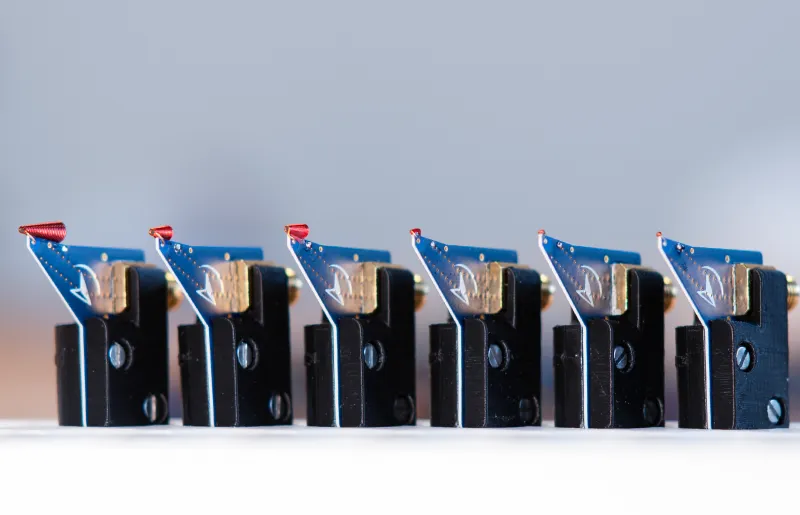
Our hardware is designed for sub-nanosecond timing and precise spatial resolution. When paired with the Tombak trigger specialist (10 ps resolution), you can reliably hit specific clock cycles even on targets with fast internal frequencies.
Single faults are often caught by modern hardware countermeasures. A double-injection setup allows you to use the first pulse to bypass a security check or "mute" a sensor, and the second to execute the actual exploit, such as instruction skipping or bit-flipping.
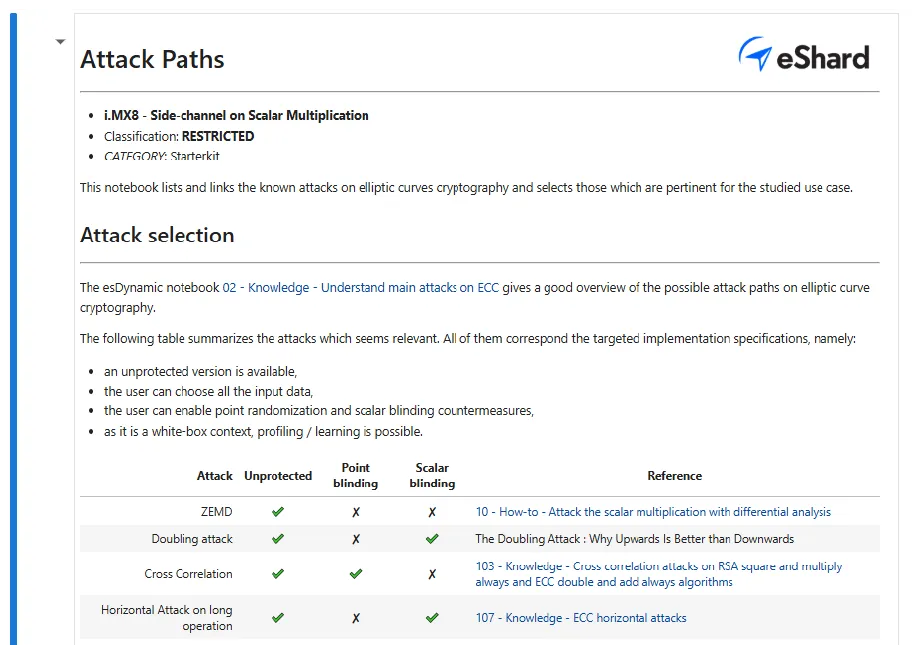
Starter kits provide a complete "lab-in-a-box" to bridge the gap between theory and practice. You receive the specific target hardware (like the i.MX8 motherboard and SOMs), the software environment, and executable notebooks that guide you from initial characterization to full key recovery using real-world datasets.