Security investigations for critical missions
A complete platform for security investigations of digital objects that brings tools, knowledge and teams together. Empower your experts with software and hardware security assessments.

Power your investigations with esReverse








Security investigations for critical missions.
A complete platform for security investigations of digital objects that brings tools, knowledge and teams together. Empower your experts with software and hardware security assessments.
Collaborative Solutions for Security Investigations
Work in a single environment where every investigation stays organized and traceable in its own project, with dedicated datasets, tools, findings, and team access.
Software
Investigations
All-in-one platform for Software Investigations
Disassemble, decompile, and debug in one platform built for advanced reverse engineering and collaborative software analysis.
Bring your debuggers and disassemblers, and enhance your analysis with our iOS and Android emulators and Time Travel Debugging tool.
Keep your analyses organized and shareable, and tap into our catalog of techniques and attack patterns to support you at every stage.
Oversee multiple projects and teams at once with full visibility into progress, assignments, and resources across all investigations.


Hardware
Investigations
All-in-one platform for Hardware Investigations
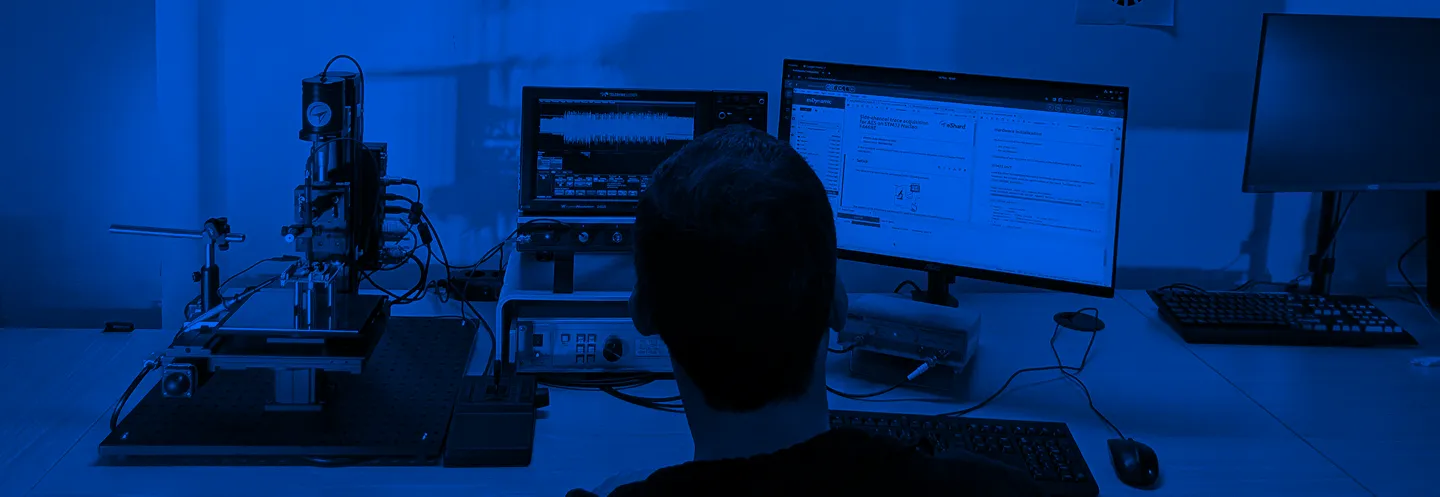
Connect your lab, run physical attacks on hardware, and share your findings in one collaborative environment.
Control your lab remotely and let teams work on the same equipment at the same time.
Integrate any vendor's equipment and customize the platform with your own libraries and functions.
Access our attack catalogue with ready-to-use scripts and proven techniques, built from years of R&D and continuously updated.
Oversee multiple security projects at once with visibility into team assignments, lab resources, and testing progress across all investigations.



Software & Hardware Security Services
Our specialists deliver tailored security services using the proven methodologies and tools we've refined through years of real-world investigations.
Need expert support ?



Software Security Assessment
Assess the security of your software to identify bugs and vulnerabilities and validate protections.
Hardware Security Assessment
Evaluate your device in our high-end lab and receive results you fully own and can replay anytime.
Security Training & Coaching
Develop your team's skills with hands-on training in reverse engineering and hardware security testing.
Industry
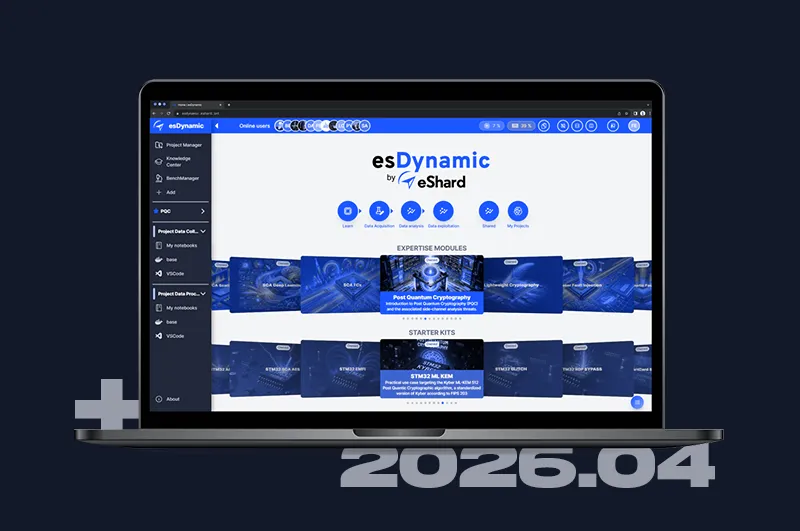
"eShard’s esDynamic unifies our characterization work into a single, high-performing framework. It gives us ultimate confidence in the long-term security and resilience of our products."
Lab
"Working with eShard enhances our cybersecurity evaluations of semiconductors. This allows us to better support global manufacturers in developing trustworthy, compliant connected products."
Institutions
"eShard made our evaluations significantly more structured and efficient. By streamlining analysis and reducing manual effort, the platform and their highly responsive support team have accelerated our work and elevated the quality of our results."
Agencies
"Before, we were mostly outsourcing the investigation, meaning we were designing in the blind. We now have a full platform that enables rapid iteration of our prototypes, allowing us to move faster and derisk the overall project schedule."
Industry
"esReverse feels like magic to us. Its capabilities are on a whole different level compared to any other tools we know and it’s continually saving us valuable hours and days where time is critical."
Expertise
Lab
"Working with eShard enhances our cybersecurity evaluations of semiconductors. This allows us to better support global manufacturers in developing trustworthy, compliant connected products."
Government Agencies
"Before, we were mostly outsourcing the investigation, meaning we were designing in the blind. We now have a platform that enables rapid iteration of our prototypes, allowing us to move faster and derisk the overall project schedule."
Semiconductor Industry
"eShard’s esDynamic unifies our characterization work into a single, high-performing framework. It gives us ultimate confidence in the long-term security and resilience of our products."
Academic Institution
"eShard made our evaluations significantly more structured and efficient. By streamlining analysis and reducing manual effort, the platform and their highly responsive support team have accelerated our work and elevated the quality of our results."
Services Industry
"esReverse feels like magic to us. Its capabilities are on a whole different level compared to any other tools we know and it’s continually saving us valuable hours and days where time is critical."
















Learn from
Technical Articles
Looking for cybersecurity expertise for your project?
Looking for cybersecurity expertise for your project?

.webp)