One environment for all investigations

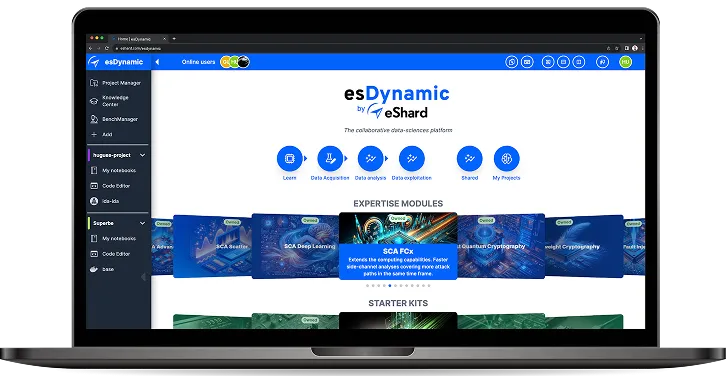
Unified Workflow
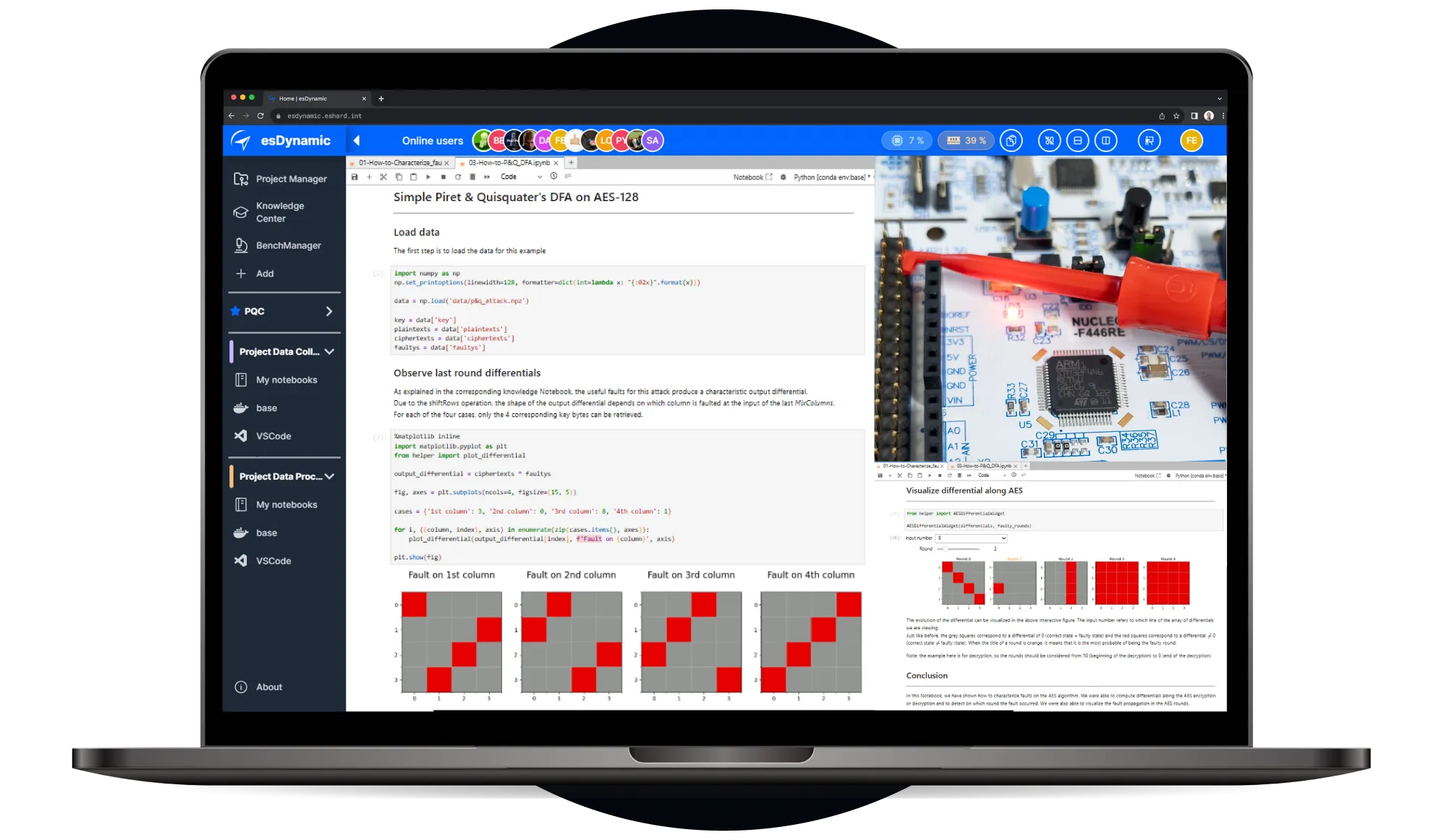
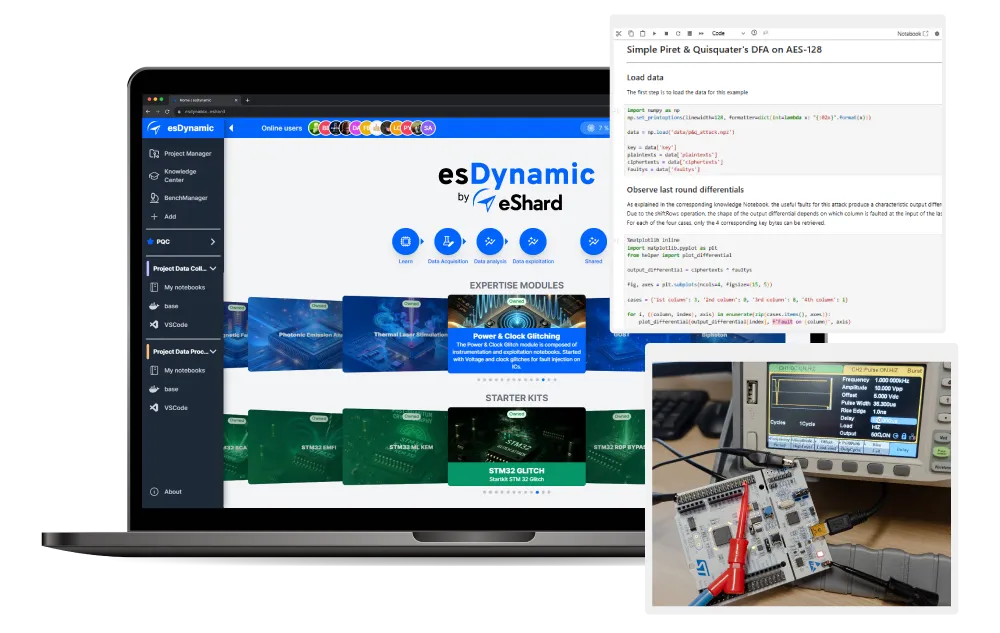
esDynamic connects your hardware, your team, and your methodology into a single platform. Acquisition signals, glitch parameter sweeps, fault analysis, and full exploitation campaigns run in the same environment.
Automated Campaigns
Ready-to-use Jupyter notebooks for spatial cartography, parameter mapping, and multi-fault injections. Automate campaigns and generate visual heatmaps to eliminate test coverage blind spots.
Hardware-Agnostic Integration
Pilot your existing bench gear, power supplies, signal generators, oscilloscopes, from any vendor alongside eShard hardware via a single unified interface.
Collaborative Data Workspace
Jumpstart your campaigns with ready-to-use Jupyter notebooks, designed to guide you through parameter mapping, and multi-fault injections.
Start from proven methodologies
Access ready-to-use security methodologies, extend them with your own findings, and build reusable attack templates that empower your entire reverse engineering team.
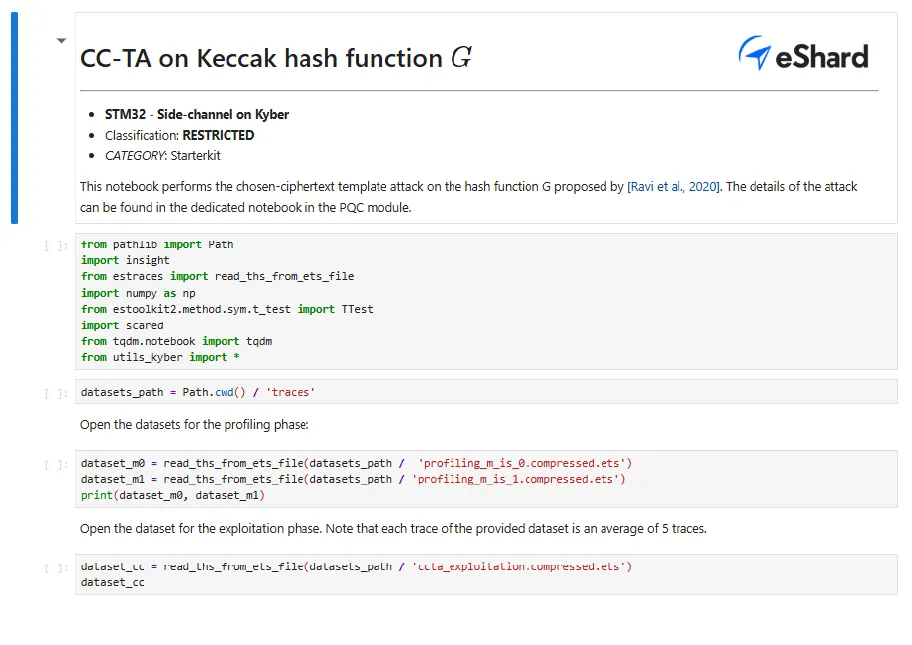
Readout protection bypass — STM32
Glitch ST's System Memory Bootloader to defeat flash readout protection. Covers MCU configuration, hardware setup, and the full parameter sweep needed to access protected flash content.
AES key recovery — i.MX8 SoC
Apply power and clock glitching to a smartcard target. Characterize fault sensitivity, explore attack scenarios, and recover AES key material from a real smartcard implementation.
On-Demand Glitching Fault Injection Expertise
Hardware Security Assessment
Experienced analysts stress-test your secure elements and FPGAs against power and clock perturbation. Deliverables include actionable mitigations and replayable proof-of-concept notebooks.
Security Training & Coaching
Remote or onsite coaching from basic glitching concepts through fully automated, high-speed campaign execution. Accelerate your team's proficiency on real hardware.
Upgrade Your Glitch Hardware Security Lab
Discuss your current lab setup, specific target architectures, or upcoming hardware evaluation projects with our engineering team.
Frequently Asked Questions
esDynamic is a unified platform that directly supports voltage glitching, clock glitching, Electromagnetic Fault Injection, Laser Fault Injection, Side-Channel Analysis, and Photoemission setups. It centralizes all your hardware, tools, experts, and your entire workflow into a single, cohesive environment.
The platform automates the process of exploring the glitch space. Analysts use ready-to-run Jupyter notebooks to perform glitch parameter sweeps—systematically adjusting the delay (trigger offset), pulse width, and amplitude / depth—to overcome system jitter and identify the exact parameters that cause exploitable faults.
By tuning the glitch parameters, analysts can induce a variety of hardware-level faults to match their theoretical fault models. Common outcomes include forcing instruction skips to bypass password checks, Program Counter (PC) corruption for privilege escalation, and precise data corruption (bit flips) required for cryptographic attacks.
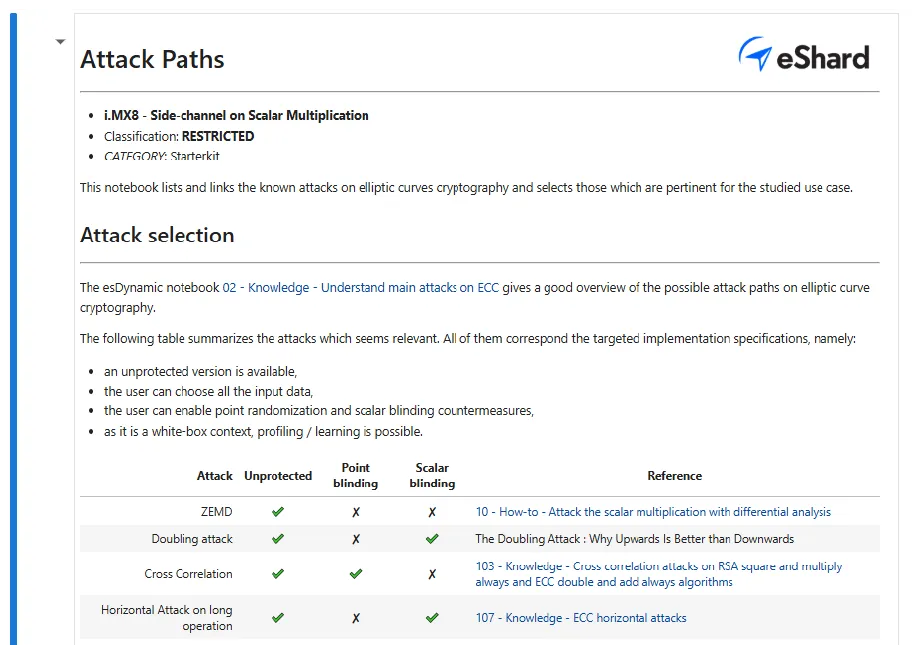
Starter kits provide a complete "lab-in-a-box" to bridge the gap between theory and practice. You receive the specific target hardware (like the i.MX8 motherboard and SOMs), the software environment, and executable notebooks that guide you from initial characterization to full key recovery using real-world datasets.