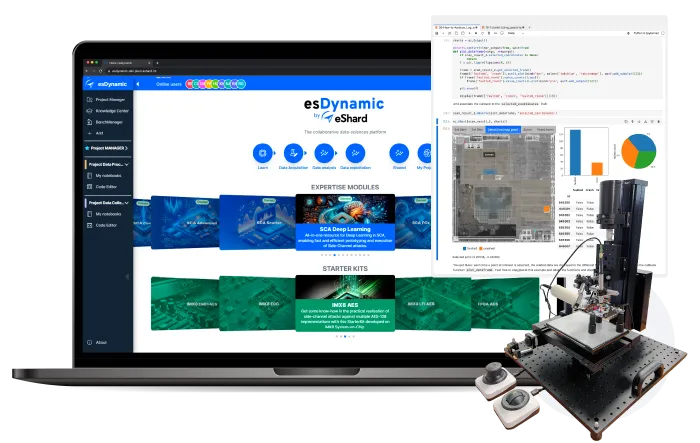
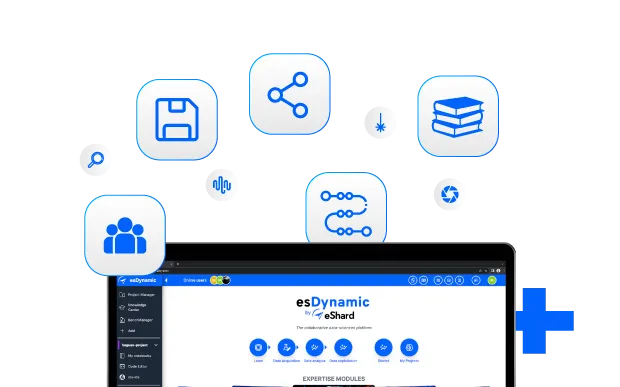
One environment for all investigations

Project-based organization
Each investigation is a project with its own datasets, tool configurations, team access, and findings. Switch between analyses without rebuilding your environment.
Open data science
environment
Leveraging JupyterLab technology, develop and bring your own scripts, your analysis is a notebook. Connect to your computing infrastructure, using server, GPUs or distributed solutions. The platform adapts to your methodology, not the other way around.
Agnostic hardware
instrumentation
Integrate and control any hardware setup. Oscilloscopes, fault injectors, probes, or custom equipment all fit into the same workflow, accessible remotely by multiple analysts.
Source of incremental
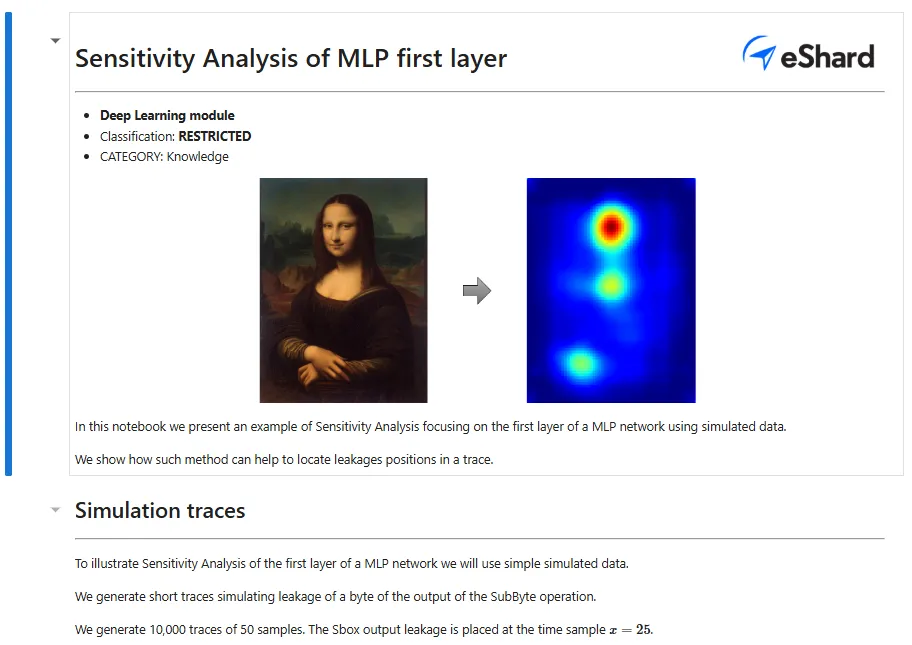
knowledge
Leverage our ready-to-use knowledge notebooks built from real-world attacks. Execute automated campaigns, reuse existing workflows, and extend them with your own work.
Complete solutions for hardware investigations
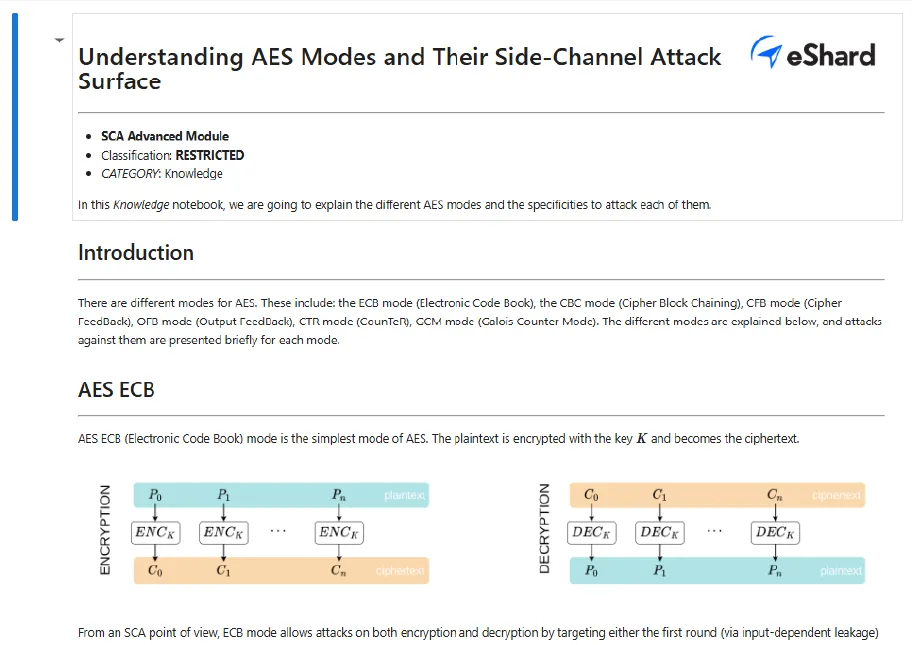
Side-channel Analysis
Investigate the cryptographic implementations against side-channel through data acquisition, data processing, and statistical analysis workflows.



Voltage Glitching
Test chip resilience through controlled power and clock perturbation.



Electromagnetic Fault Injection (EMFI)
Induce faults through EM pulses with spatial and temporal control.



Laser Fault Injection (LFI)
Advanced optical fault injection with backside imaging and laser pulse control.




Photonic Emission Analysis
Investigate chip behavior and security through photon emission patterns for non-invasive security assessment and attack validation.




Physical attacks without
physical test bench.
Execute software binaries into an emulated environment (Arm, Intel, RiscV), fault them, collect traces and make side-channel and fault injection analysis on these traces. Ideal for root cause analysis.

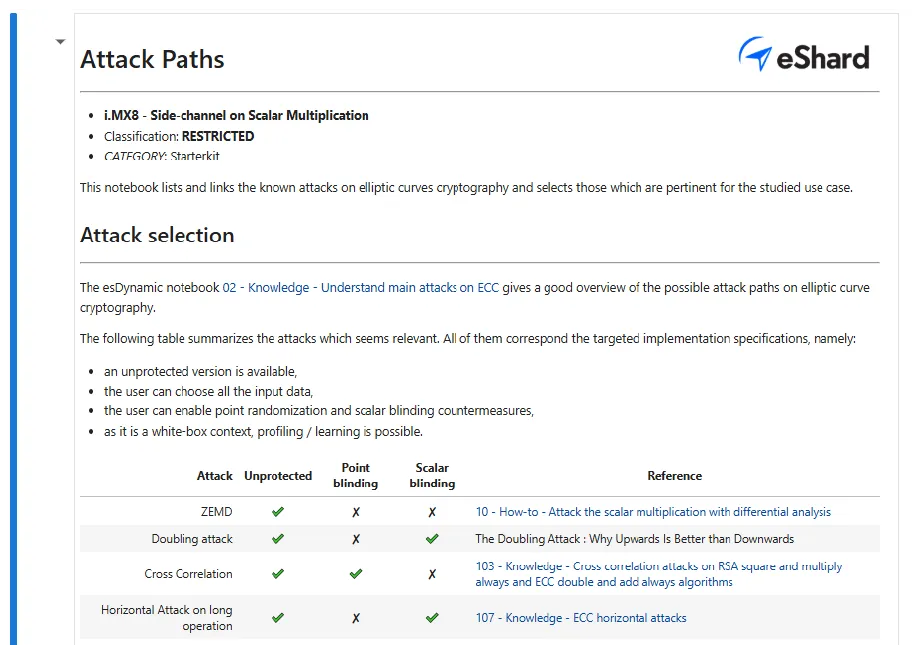
Start from proven methodologies
Integrate years of side-channel R&D into your workflow with executable attack catalogs and starter kits to reproduce attacks and analyze leakage.
Advanced Side-Channel Analysis
Target the dedicated ARMv8 AES instruction set on a Cortex-A53 core to retrieve secret keys via side-channel analysis.
Post-Quantum Cryptography (PQC)
Defeat register randomization mitigations on a 50k-cell FPGA using advanced EM-based side-channel techniques.
Start investigations with esDynamic from day 1
Tell us about your targets and attack requirements. We'll help you set up the right lab configuration and platform access.
Frequently Asked Questions
From a single interface, you can perform Side Channel Attacks (SCA), Fault Injection (LFI, EMFI, Voltage/Clock Glitching), and Failure Analysis, including Photoemission.
Mostly no. Once the device (DUT) is manually placed on the bench, analysts can remotely control test equipment and launch acquisitions through the esDynamic server and esBox gateway.
It scales with your IT infrastructure. esDynamic natively integrates with distributed computing and GPUs to process massive datasets and execute algorithms without bottlenecks.
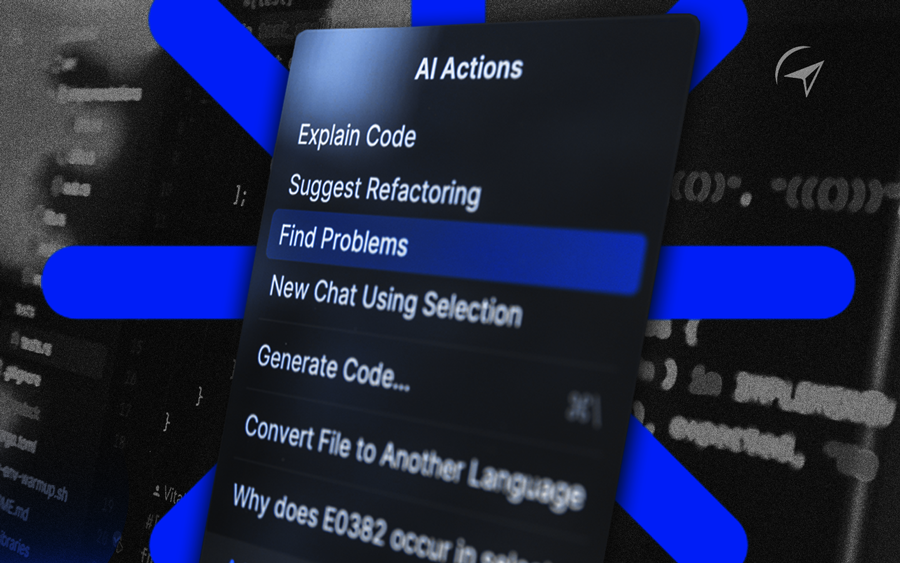
Yes, with no restrictions. Because it is built on standard Python and Jupyter notebooks, you can seamlessly run your custom scripts alongside our built-in libraries.