ALL-IN-ONE PLATFORM
esDynamic
Manage your attack workflows in a powerful and collaborative platform.
Expertise Modules
Executable catalog of attacks and techniques.
Infrastructure
Integrate your lab equipment and remotely manage your bench.
Lab equipments
Upgrade your lab with the latest hardware technologies.
PHYSICAL ATTACKS
Side Channel Attacks
Evaluate cryptography algorithms from data acquitition to result visualisation.
Fault Injection Attacks
Laser, Electromagnetic or Glitch to exploit a physical disruption.
Photoemission Analysis
Detect photon emissions from your IC to observe its behavior during operation.
EXPERTISE SERVICES
Evaluation Lab
Our team is ready to provide expert analysis of your hardware.
Starter Kits
Build know-how via built-in use cases developed on modern chips.
Cybersecurity Training
Grow expertise with hands-on training modules guided by a coach.
ALL-IN-ONE PLATFORM
esReverse
Static, dynamic and stress testing in a powerful and collaborative platform.
Extension: Intel x86, x64
Dynamic analyses for x86/x64 binaries with dedicated emulation frameworks.
Extension: ARM 32, 64
Dynamic analyses for ARM binaries with dedicated emulation frameworks.
DIFFERENT USAGES
Penetration Testing
Identify and exploit system vulnerabilities in a single platform.
Vulnerability Research
Uncover and address security gaps faster and more efficiently.
Code Audit & Verification
Effectively detect and neutralise harmful software.
Digital Forensics
Collaboratively analyse data to ensure thorough investigation.
EXPERTISE SERVICES
Software Assessment
Our team is ready to provide expert analysis of your binary code.
Cybersecurity training
Grow expertise with hands-on training modules guided by a coach.
INDUSTRIES
Semiconductor
Automotive
Security Lab
Gov. Agencies
Academics
Defense
Healthcare
Energy
ABOUT US
Why eShard?
Our team
Careers
FOLLOW US
Linkedin
Twitter
Youtube
Gitlab
Github
Fault Attacks on SPHINCS+ | Expert Review #3

Introduction
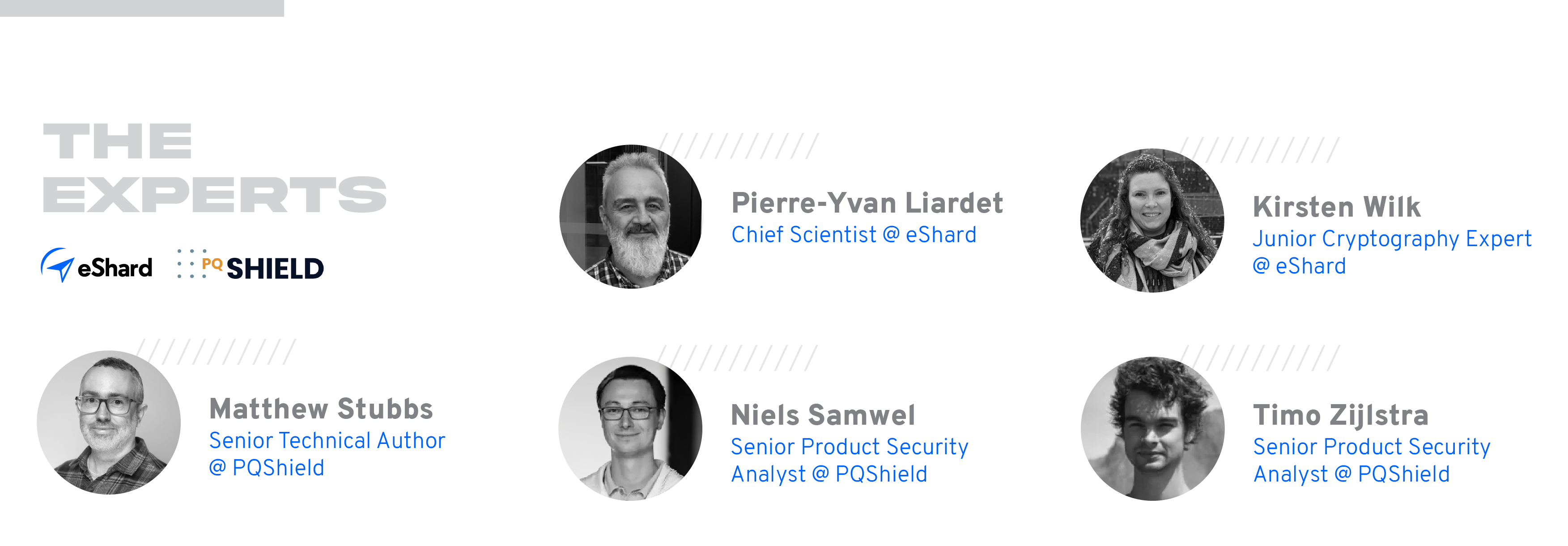
Welcome back to the Expert Review series, where, together with PQShield, we delve into the dynamic world of cybersecurity to bring you unbiased and detailed analyses from seasoned professionals. If you missed our second edition, check it out here.
In this review, we look back at CHES 2023, the 25th edition, focusing on the presentation given by Aymeric Genêt: “On Protecting SPHINCS+ Against Fault Attacks”. The concept of Genet’s presentation takes advantage of a generic fault injection method that threatens implementations of the coming NIST Post Quantum Cryptography standard SLH-DSA, Stateless Hash-Based Digital Signature Standard FIPS-205 (SPHINCS+).
About the paper
This notable research critically examines countermeasures proposed to withstand fault attacks on SPHINCS+ introduced in 2018 by Castelnovi et al. and some possible improvements. The major contribution is the impact on protecting the implementation of this hash-based post-quantum cryptographic signature. Let’s dive in.
Our Expert Review
What was studied?
The paper, “On Protecting SPHINCS+ Against Fault Attacks'' is a report on a fault analysis study on SPHINCS+ completed during the author's PhD program. In particular, the author aimed to find effective countermeasures for the devastating fault injection attack from 2018 by Castelnovi, Martinelli, and Prest, “Grafting Trees: a Fault Attack against the SPHINCS framework”. However, the author concludes that he was unable to find any efficient countermeasure, and that this attack can be applied to any of the SPHINCS variants...
Why is it important?
The potential impact of the studied fault attack is devastating because of its practicality, and due to the difficulty of protecting against it. The author states that at the current time, no practical countermeasures against this attack exist, with the exception of the complete re-computation of the signature.
Put simply, this is potentially a disastrous vulnerability that’s important to be aware of for anyone implementing any of the SPHINCS variants. It underlines the idea that hash-based signature generation is not recommended for use in hostile environments, and that the use case for hash-based signature schemes in constraint devices should instead be limited to verification of signatures generated in secure environments.
Which new insights have been contributed, and how significant are they?
The fault attack from “Grafting Trees: a Fault Attack against the SPHINCS framework” is expanded and extensively analysed, showing the impact of fault injection on all the components and subtree layers of the signature generation. The author analyses the verifiability and exploitability of faulted signatures, and shows that exploitable faulty signatures can, with some probability, still be verified as valid by the verification procedure. This complicates fault detection, leading the author to investigate different countermeasures based on caching of intermediate values. However, the memory cost of such countermeasures turns out to be prohibitive, while providing only limited protection.
How practical are the results?
A very weak fault model is assumed, in which the attacker injects a random fault affecting the output of any one of the many hash computations during the signature generation. No precise timing or particular impact is required; the fault can be injected anywhere during the signature generation, causing a bit flip, zeroization, instruction skip, or any other effect. With a high probability (>90%), such a fault results in a signature that can be exploited to forge signatures. This means that the attack can be performed with low-cost fault injection equipment. An argument could be made that even an accidental fault, caused by software or hardware failure, might pose a threat in real-world applications. The author urges that redundancy checks, such as signature re-computation, be implemented, even if the use case does not take fault attacks into account, such as signatures for firmware updates.
When might the impact happen?
In 2023, NIST published a first draft of SLH-DSA [FIPS 205], a standardised description of the SPHINCS+ algorithm. Since SPHINCS+ was chosen to be standardised by NIST as a result of the ongoing PQC standardisation program, any and all cryptanalysis is very relevant now and will continue to be in future. When the finalised NIST specifications are published (expected imminently), the scheme will be widely used.

What’s next?
The fault attack vulnerability of hash-based signature schemes, and the difficulty in protecting against those attacks, is different to vulnerabilities affecting other digital signature schemes. While there is much confidence in the theoretical security of hash-based signatures, it is hard to implement them securely. This work highlights the need for further research into potential countermeasures against fault injection.
For now, the absence of effective countermeasures highlights that SPHINCS+ might not be suitable for use cases prone to fault attacks during signature generation. For those use cases, ML-DSA [FIPS 204, Dilithium] would be easier to protect.
Stay tuned for more reviews of other groundbreaking articles as we delve deeper into the advancements and challenges in the field of cryptography. The journey towards securing our digital infrastructure is ongoing, and we are committed to bringing you the latest insights and analyses from the forefront of cryptographic research.